Recommended
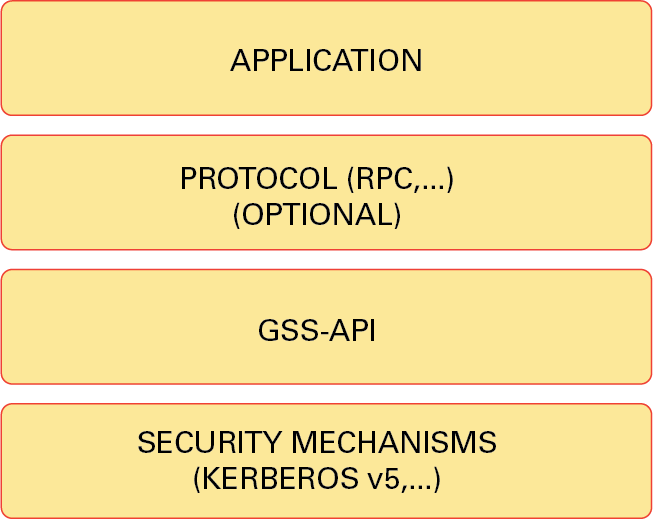
Sometimes your computer may display a message that the Solaris server encountered a gss API error. This problem can have several causes.
1) Replace the /etc/krb5/krb5.conf file with any reference to the vas.conf file. The vas.conf file contains kerberos settings, which apparently can be used by ssh with other applications that support kerberos. The krb5.conf document might be in a different area for a different operating system.
# mv /etc/krb5/krb5.conf /etc/krb5/krb5.conf.sav (if krb5.conf exists)
# ln -h /etc/opt/quest/vas/vas.conf / etc./krb5/krb5.conf
and restart sshd. There may be other GSS-API bugs that need to be fixed as well. our vas.conf documentation covers all Kerberos options.
Add the following two sets of ssh_config and sshd_config for each affected hosting provider to disable the GSS-API in ssh:
and system sshd. This will also disable any single sign-on usage for that SSH connection, which can often be taken into account in some environments.
I have developed a new container/zone in Solarist (Sparc) and am using Centrify available for AD LDAP authentication. My favorite ssh client is the following
Recommended
Is your PC running slow? Do you have problems starting up Windows? Don't despair! Fortect is the solution for you. This powerful and easy-to-use tool will diagnose and repair your PC, increasing system performance, optimizing memory, and improving security in the process. So don't wait - download Fortect today!

I see strange ssh behavior. When I ssh into a new zone that other people (non-root users)accessed from somewhere else or from the zone itself, I get the following error:
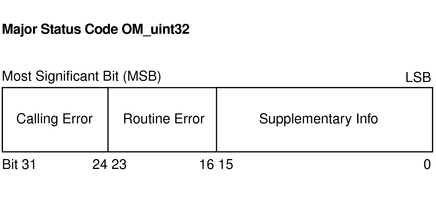
There was a real GSS-API error on the server; connection becomes analog (851968/0):
Undefined GSS error. Minor code may shed more light
No errors
Use the GssKeyEx parameter to disable GSS-API key switching and try again.
Outage: Previously, the server encountered a GSS-API error during an SSHv2 key exchange covered by the GSS-API
The problem does not occur when I SSH into the zone from root, OR when I use the host’s IP address instead of the hostname. I just have a problem with remote SSH – only when I arrive.
Sun_SSH_1.1.1, SSH methods 1.5/2.0, OpenSSL 0x0090704f
debug1: config read info /etc/ssh/ssh_config
debug1: Rhosts authentication disabled, source port definitely not trusted.
debug1: ssh_connect: needpriv 0
debug1: connecting to Balloonv1 [10.38.35.100], entry 22.
debug1: connection established.
debug1: identity file /users/cmorgan/.ssh/identity Version -1
debug1: identification file /users/cmorgan/.ssh/id_rsa category -1
debug1: identity file /users/cmorgan/.ssh/id_dsa type -1
debug1: remote protocol version 2.0, remote software production Sun_SSH_1.1.1
debug1: Mapped: Sun_SSH_1.1.1 with Sun_SSH_1.1.1*
debug1: enable protocol compatibility mode 2.0
debug1: local version string SSH-2.0-Sun_SSH_1.1.1
debug1: use_engine is indeed “yes”
debug1: pkcs11 core initialized, this tool now uses RSA, DSA as well as symmetric ciphers by default
debug1: pkcs11 module initialization complete
debug2: kex_parse_kexinit: diffie-hellman-group-exchange-sha1, diffie-hellman-group1-sha1
debug2: kex_parse_kexinit: ssh-rsa, ssh-dssdebug2: kex_parse_kexinit: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: en-AU
debug2: kex_parse_kexinit: en-AU
debug2: kex_parse_kexinit: first_kex_follows 0
debug2: kex_parse_kexinit: 0 ok
debug1: ssh_gssapi_init_ctx(706a8, ballonv1, 0, three, ffbff714)
debug3: ssh_gssapi_import_name: snprintf() returned 14, possibly 15
debug2: GSS-API engine coded as WM5Slw5Ew8Mqkay+al2g==
debug1: SSH2_MSG_KEXINIT sent
debug3: kex_reset_dispatch – Should I personally use dispatch_set(KEXINIT) here? 0 && !0
debug1: SSH2_MSG_KEXINIT received
debug2: kex_parse_kexinit: gss-group1-sha1-toWM5Slw5Ew8Mqkay+al2g==,diffie-hellman-group-exchange-sha1,diffie-hellman-group1-sha1
debug2: kex_parse_kexinit: ssh-rsa, ssh-dss, null
debug2: kex_parse_kexinit: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: en-AU
debug2: kex_parse_kexinit: en-AU
debug2: kex_parse_kexinit: first_kex_follows 0
debug2: kex_parse_kexinit: reserved 0
debug2: kex_parse_kexinit: gss-group1-sha1-toWM5Slw5Ew8Mqkay+al2g==,diffie-hellman-group-exchange-sha1,diffie-hellman-group1-sha1
debug2: kex_parse_kexinit: ssh-rsa, ssh-dssdebug2: kex_parse_kexinit: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: kex_parse_kexinit: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc
debug2: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: no, zlib
debug2: kex_parse_kexinit: en-AU, en-NZ, i-default
debug2: kex_parse_kexinit: en-AU, en-NZ, i-default
debug2: kex_parse_kexinit: first_kex_follows 0
debug2: kex_parse_kexinit: reserved 0
debug2: mac_init: stumbled upon hmac-md5
debug1: kex: server->client aes128-ctr hmac-md5 none
debug2: mac_init: found hmac-md5
debug1: kex: client->server aes128-ctr hmac-md5 no
debug1: recommended long tags sent by peers, ctos: en-AU, en-NZ, i-default
debug1: Peer sent suggested lengths Tags, Stoc: en-AU, en-NZ, i-default
debug1: we accepted long tags, ctos: en-AU
debug1: We suggested long tags, stoc:en-AU
debug1: agreed language: en-AU
debug1: dh_gen_key: important priv bits set: 119/256
debug1: bits set: 497/1024
debug1: call gss_init_sec_context
debug1: ssh_gssapi_init_ctx(d2458, ballonv1, 1, 0, ffbff7d4)
debug3: ssh_gssapi_import_name: snprintf() returned 20, expected 15
debug1: Remote: agreed base location: en_AU.UTF-8
debug1: Remote: locale for consistent messages: en_AU.UTF-8
debug1: KEXGSS_HOSTKEY received
There was a nice bug in the GSS-API server; the connection will be closed (851968/0):
Undefined GSS error. Helper code can generate more information
No errors
Use the GssKeyEx parameter to permanently disable and retest GSS-API key exchange.
Shutdown: The server encountered a GSS-API GSS-API error during a serious SSHv2 secure exchange
debug1: call cleanup 0x348a4(0x0)
Oddly enough, when I run kdestroy, I can ssh successfully, but only for that membership session.
“x2100 server with Solarist 5 installed
Version: .10
Core architecture: i86pc
Application architecture: i386
Kernel version: SunOS 5.10 Generic_127128-11
I have a full pair server on which I want to enable ssh without a password. Servers A and . The target system (server B) is the above reason. (I sshed into another server without a password, so everything works fine from the server)
I checked a few things
I have obtained public and private rsa recommendations and have added the public key to the author_keys file often in the ~
I verified that your user is not nologin, secure, or nopasswd by running passwd -erinarians
I’ve SSHed to a different troubleshooting port to check the drive and find the problem.
[
debug1: sshd version Sun_SSH_1.1
debug1: PEM private key read completed: RSA
debug1: enter host private key: #0 option 1 RSA
debug1: Private PEM read required: type DSA
debug1: legitimate private host: #1 DSA type 2
debug1: bind and move 24 to ::.
The server continues to listen on ::Port 24.
debug1: server rarely forks when running in debug mode.
Connection caused by
debug1: clIente process version 2.0; Sun_SSH client software version_1.1
debug1: no match: Sun_SSH_1.1
debug1: enable protocol compatibility feature 2.0
debug1: local version number SSH-2.0-Sun_SSH_1.1
debug1: list_hostkey_types: ssh-rsa, ssh-dssdebug1: SSH2_MSG_KEXINIT sent
debug1: SSH2_MSG_KEXINIT received
debug1: kex: client->server aes128-ctr hmac-md5 no
debug1: kex: server->client aes128-ctr hmac-md5 none
debug1: recommended long tags sent by peer, ctos: i-default
debug1: peer sent recommended long tags, stoc:i-default
debug1: We suggested long tags, ctos:i-default
Der Solaris Server Hatte Einen Gss Api Fehler
Serwer Solaris Mial Blad Gss Api
솔라리스 서버에 Gss Api 오류가 있습니다
Solaris Server Had Een Gss Api Fout
Servidor Solaris Teve Um Erro De Api Gss
Server Solaris Imel Oshibku Gss Api
Solaris Servern Hade Ett Gss Api Fel
Le Serveur Solaris A Eu Une Erreur Api Gss
Il Server Solaris Ha Avuto Un Errore Api Gss
El Servidor Solaris Tenia Un Error Gss Api